Internet monitoring is the act of capturing data as it travels across the internet towards its intended destination. - taken out from Privacy International’s explainer.
The internet traffic, or all your data sent and received, is broken down in parts referred to as ‘packets’. They are transferred with the Internet Protocol through a network of routers and then reassembled at their destination to become the sent data.
To transmit and receive these packets from one point to another on the internet, an infrastructure that involves physical transmission lines and electronic systems play a role. So, the Internet monitoring can take place across any point of this infrastructure, depending on what information is trying to be collected.
The OSI model
For those ‘packets’ to be created they have to go through seven layers of the Open Systems Interconnection (OSI) Model:
- Application
- Presentation
- Session
- Transport
- Network
- Data Link
- Physical
Internet monitoring focuses on the interception of packets of information transmitted across this Model. Although content of the data is best to be gathered at the Application layer the diagram shows that it can be gathered at nearly every level of the internet. It can be the content itself or the metadata. Metadata can be gathered at close to every point in the OSI Model, however content can even be gathered too. Each layer from Data Link to Session provides different kinds of information as our packets travel through the network.
At the physical layer, substantial hardware needs to be in place to gather information and requires a greater degree of reconstruction of the packets than if the interception was taking place closer to the Application and Presentation level.
Lawful or Massive Interception
Lawful Interception is a legally based framework in which surveillance is conducted, targeting specific suspects and avoiding interception of other content. The other option is Massive, looking at everyone’s information as it moves through the communication framework and picking out the information relevant to the interceptor.
Communication Service Provider Monitoring
We use Service Providers in our everyday life now. When we communicate with our service provides like Google, Facebook or Skype or our email providers the servers operating the service retain and store the information, cataloguing it and tagging it.
This data doesn’t just disappear. These service providers keep it so they can better target advertisements at us: which is where many of these providers make their money. Another effect of this retention is the release of information to law enforcement or intelligence agencies.
With all the services available on the internet today, it is way much easier for Intelligence Agencies to request information us whenever they want. Even more it is the Gouvernements who control these Service Providers, and it is the Governments who the Intelligence Agencies work for. So, how hard can it be for them to get information on any email we send and receive, our chat history, our browsing habits even throughout the whole year.
Open Source Monitoring
As we don’t mind generating data on the internet, this information is gathered from a host of resources including some of the most well known and widely used social networks. Analysis is then run over the information, detecting patterns and identifying individuals across different services.
Information posted across social networks is monitored along with who is speaking to whom and the relationship between people. This then creates a broad picture of a person’s friendship network. What begins as interest in one individual quickly spirals into interest with all their contacts.
Without using software, the information would remain disparate and unconnected like the individual using the services intended. But, by analyzing it, a whole person’s life across these different networks is pulled together and presented for the user at the other end.
VoIP Monitoring
The interception of voice over internet (VoIP) is also a focus of many different surveillance technologies. The interception takes place over network operator services where the metadata and the content are separated by the VoIP terminal itself.
Metadata includes “Events” on the phone, which can include the beginning, release and attempted termination of a call, and sometimes the provision of contact information and the street address of the target.
Email Monitoring
The interception of emails over the internet can include both the content of the email and the various pieces of metadata that come with it including sender, recipient list, message ID, server addresses, status, and total recipients of the message.
The metadata is generally less protected legally than content and thus accessed easier and stored for longer. So, it can provide a greater deal of insight.
If the email messages and metadata are not encrypted on their way, the content can be read no matter where intercepted, the server, or other relay servers.
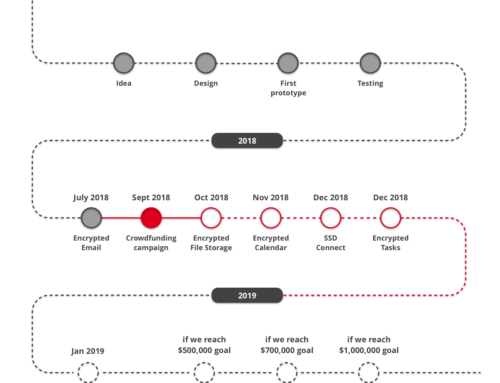
Secure Swiss Data has created encrypted email service to protect your data and secure your communication.


Leave A Comment